The 0xNickLFranklin saga continues[0]. Let us share our discovery of a full DPRK IT worker cluster centered around Aqua Protocol… and not only.
Nick L Franklin posed as a security engineer, focusing on describing simple Web3 attacks. He is most likely connected to the AppleJesus[1] threat operation run by the DPRK. This operation targets security researchers and dates as far back as 2021. Nick L Franklin revealed himself as one of the DPRK operators after attempting to deliver a malicious .app file.
[0] https://x.com/danielvf/status/1905642180749775189
[1] https://blog.google/threat-analysis-group/new-campaign-targeting-security-researchers/
Aqua Protocol Core Team
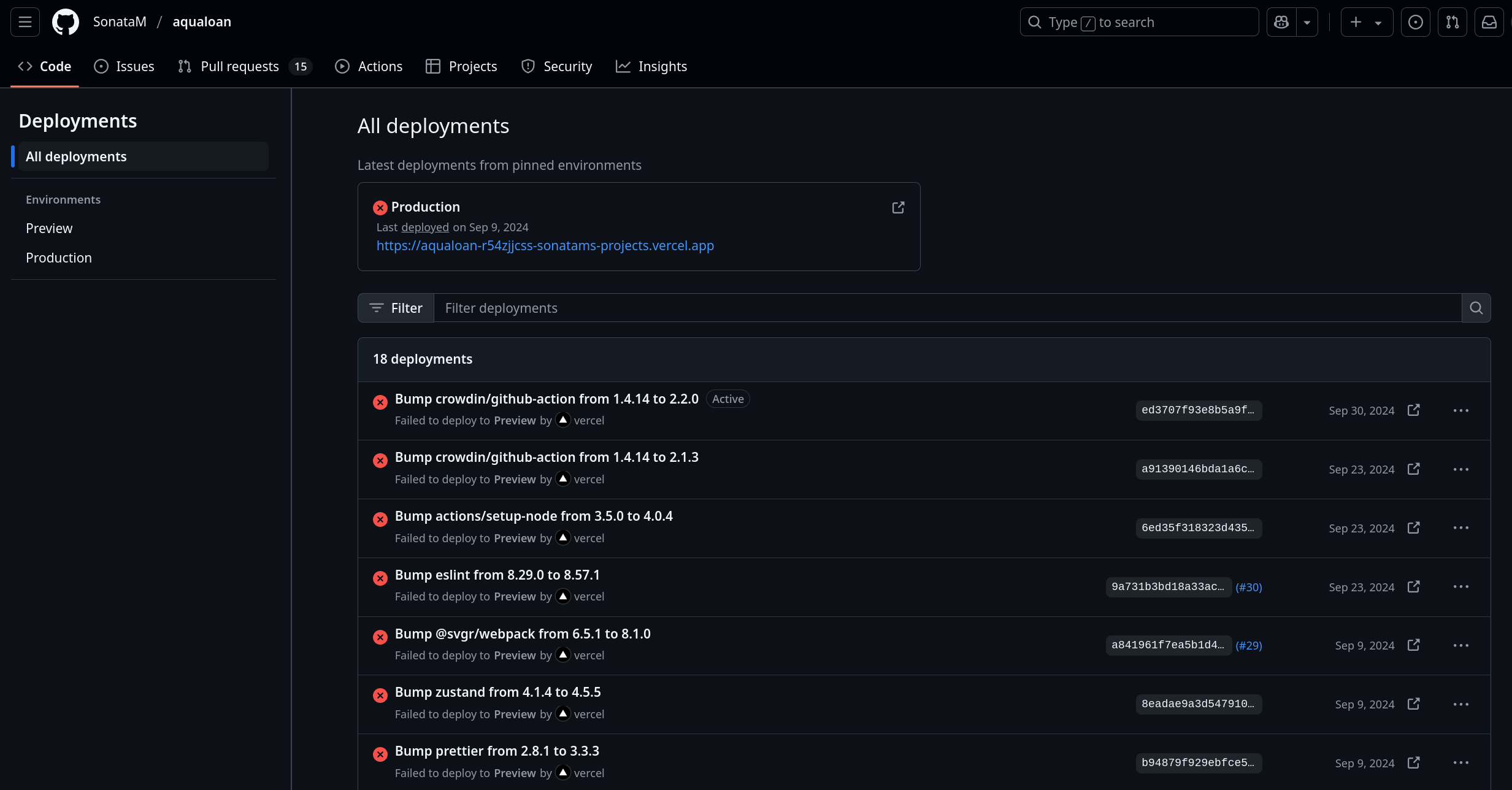
Aqua Protocol was discovered as one of the crypto operations connected to 0xNickLFranklin. This “fake” Web3 lending application, built on top of the Aave V3 architecture, has now been completely purged from existence[0]. The organization’s codebase, as well as the protocol’s liquidity (almost $800k USD, all under control of DPRK actors), have been wiped[1]. Nick was one of the two core contributors to the protocol.
- Aqua Protocol Organization:
https://github.com/techaqualoan(Removed on March 27, 2024) - Core Contributors:
https://github.com/NickLFranklin(Main actor, account removed on March 28, 2024)https://github.com/mpereiraesaa(Likely a purchased or stolen account, still active)
[0] Aqua Protocol cleanup: https://x.com/blackbigswan/status/1905216069813285189
[1] Backup screenshot view: https://x.com/blackbigswan/status/1905003831148302751
Aqua Protocol IT Workers
Most discussion around Nick L Franklin has revolved around his multiple identity rotations on different Telegram chats, paired with cold outreach campaigns targeting other engineers, protocols, and Web3 ecosystem participants. However, seeing how Ketman project is focused on Github and OSS attack vectors, we explored this vector and uncovered further connections within it. It’s worth noting this is a usual DPRK M.O. – they rarely work alone, and when one actor is found, it often leads to untangling the whole network of connected accounts. This case is no different.
Other developers connected to Aqua Protocol’s development include:
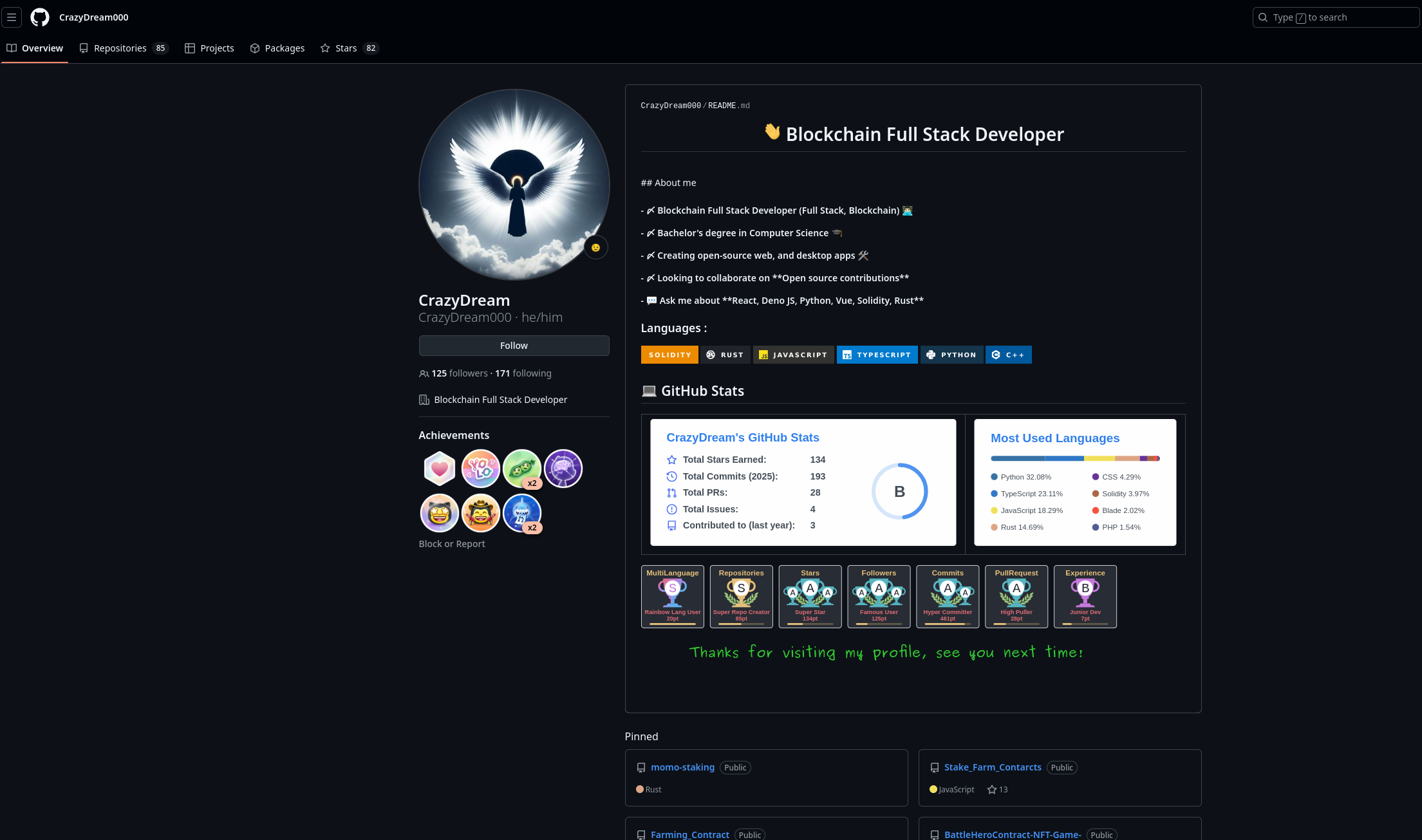
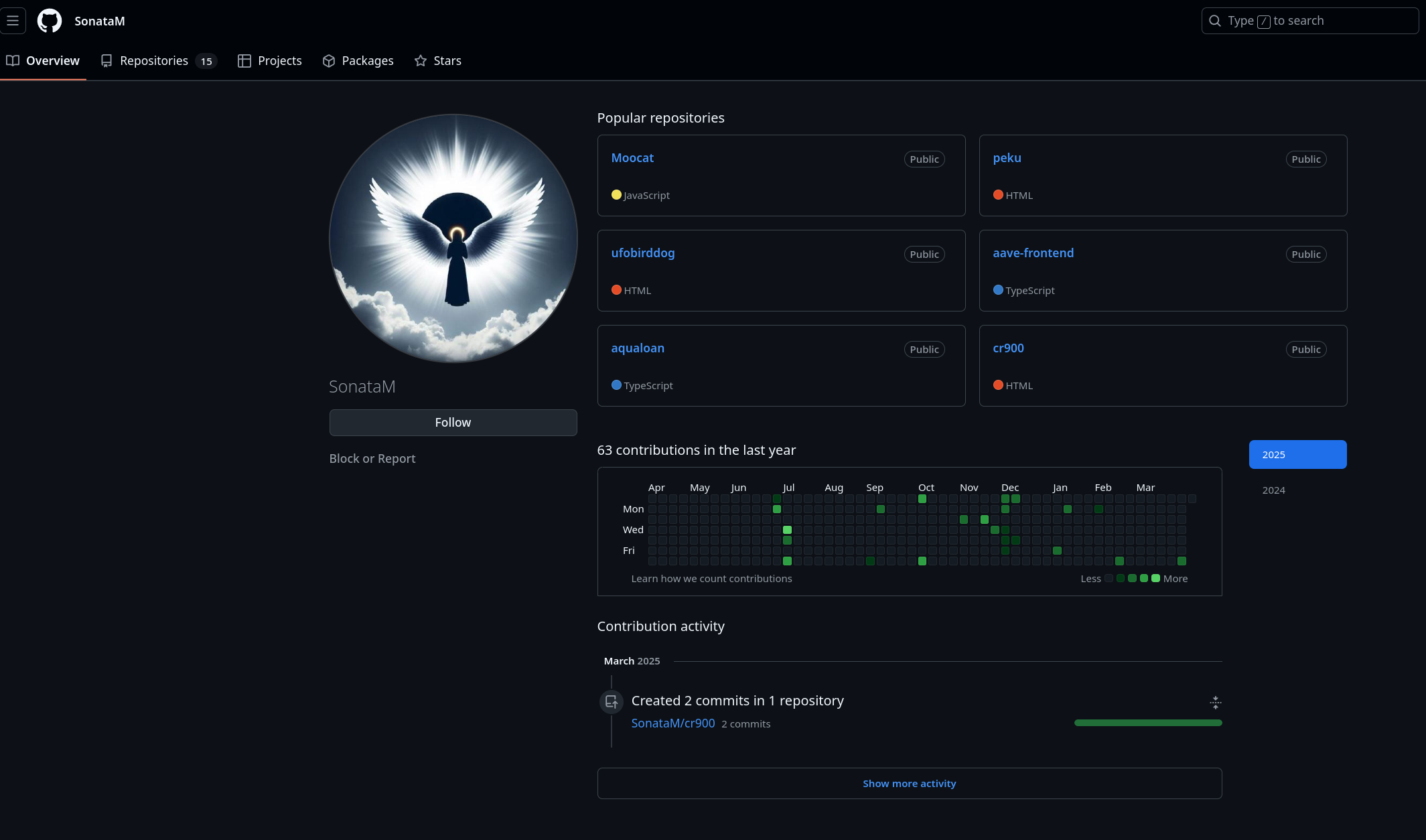
https://github.com/SonataM(The front-end developer and inital tester/deployer for Aqua Protocol)https://github.com/CrazyDream000(Alternative persona ofSonataM)https://github.com/jewelas(Account connected toCrazyDream000through common contributions)
Each of these displays a somewhat unique threat type while also being comingled within a single network.
Four North Koreans, Five Threats
-
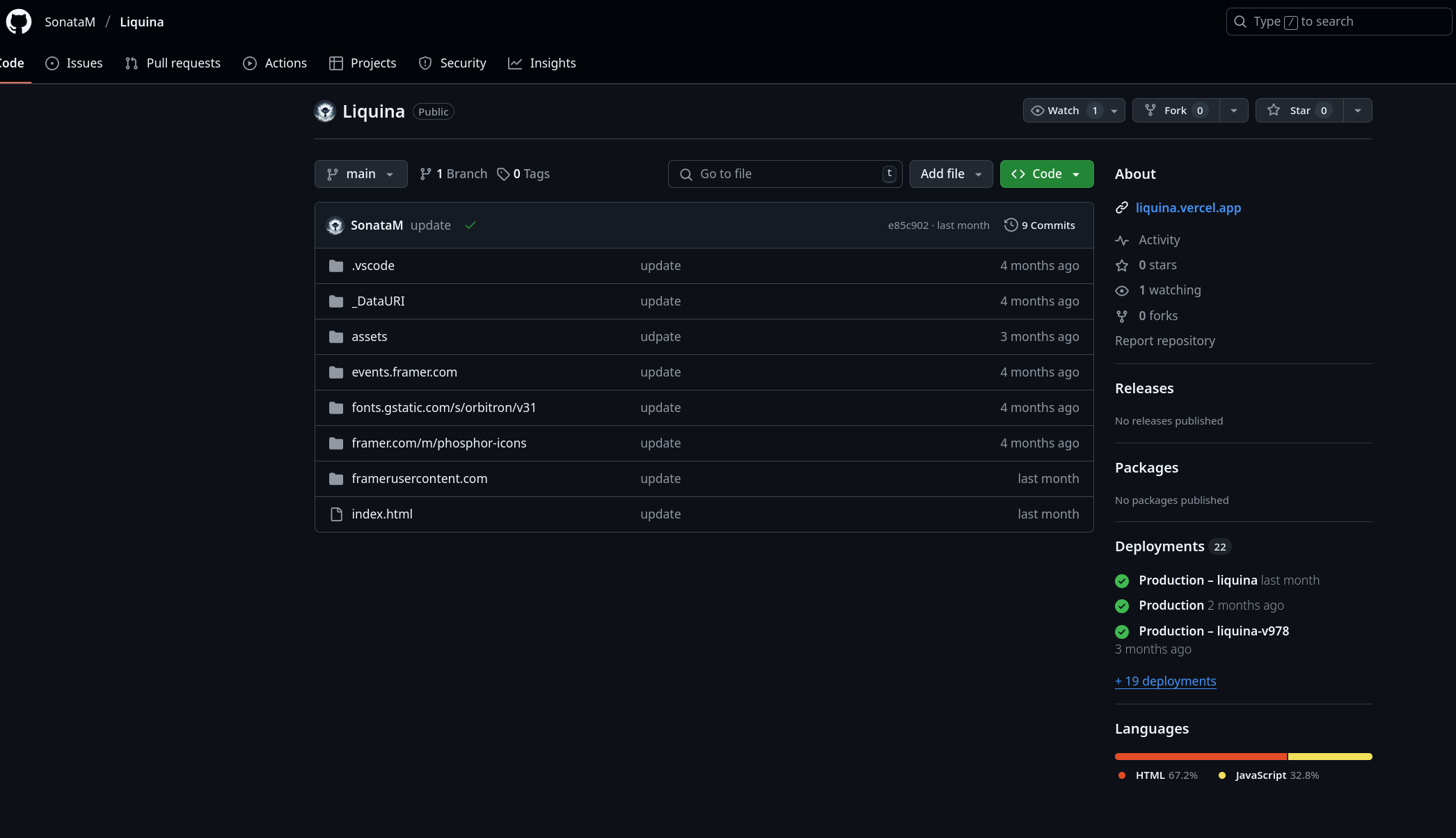
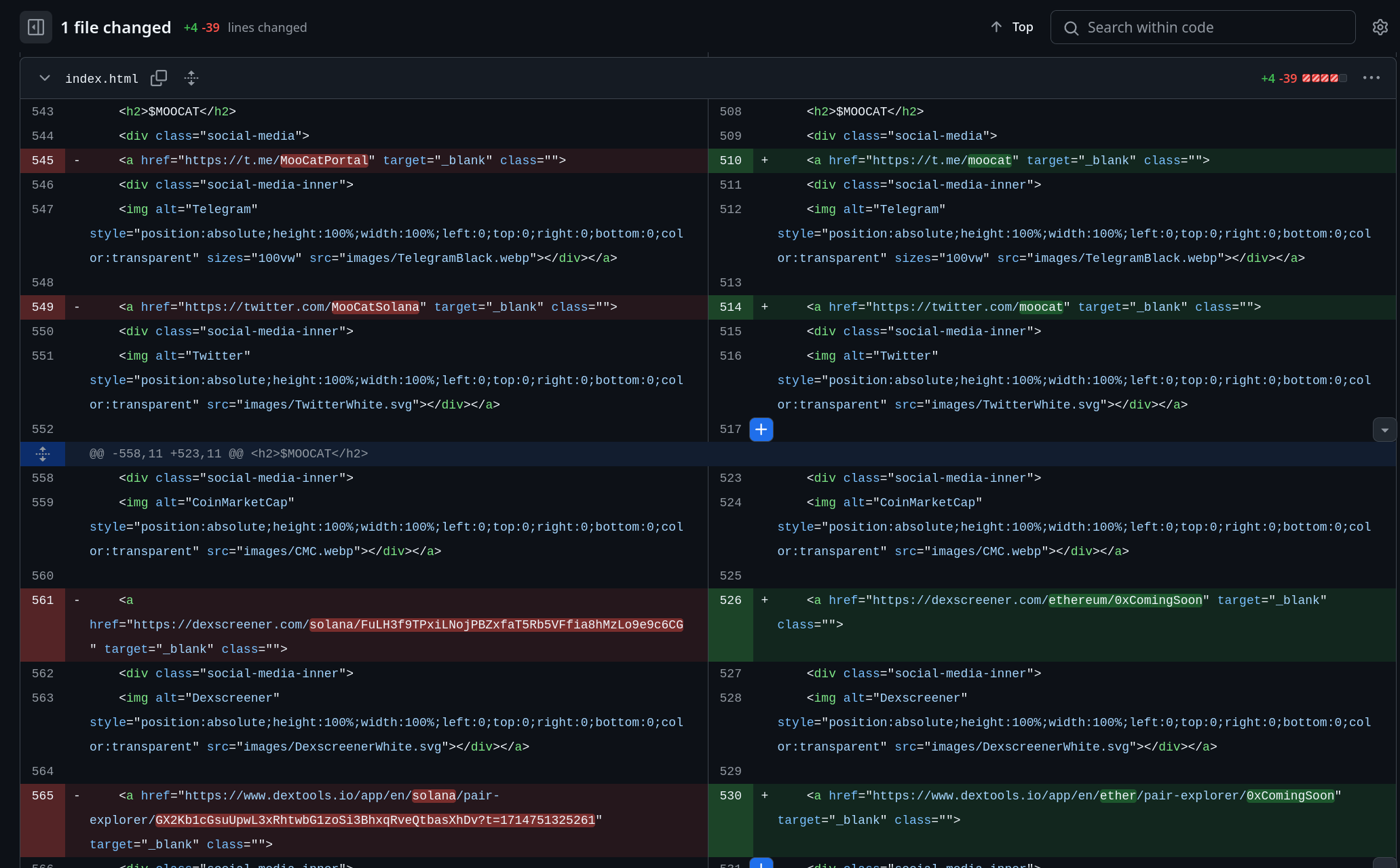
SonataM: Hosts the code for the “fake” protocolaqualoan(contracts & front end). He also hosts a large collection of copied websites (HTML code), most likely intended for use in phishing/impersonation attacks or rug pull operations. This collection includes sites seemingly related to:liquina,trumpx,brics,trumpshair,decoy,arky,orken,louie,vodcat,cr900,peku,ufobirddog,moocat.- Most of these appear to be memecoin projects across different blockchains.
- Some are “fake” versions of original projects, deployed to a different network than the original to confuse buyers.
- Others are bootstrapped rug pull-type projects. This serves as further proof that the DPRK is involved not only in hacking but also in scamming operations, leveraging their access to massive amounts of funds, which allows for the deployment of significant initial liquidity.

-
CrazyDream000: Was an extremely active actor. The account itself displays common DPRK IT worker characteristics, even aside from its connection to0xNickLFranklin.CrazyDream000committed code to at least three seemingly legitimate organizations:koinos,CarmineOptions, andprovable-things.CrazyDream000appears to be an alternative persona ofSonataM, run by the same individual. -
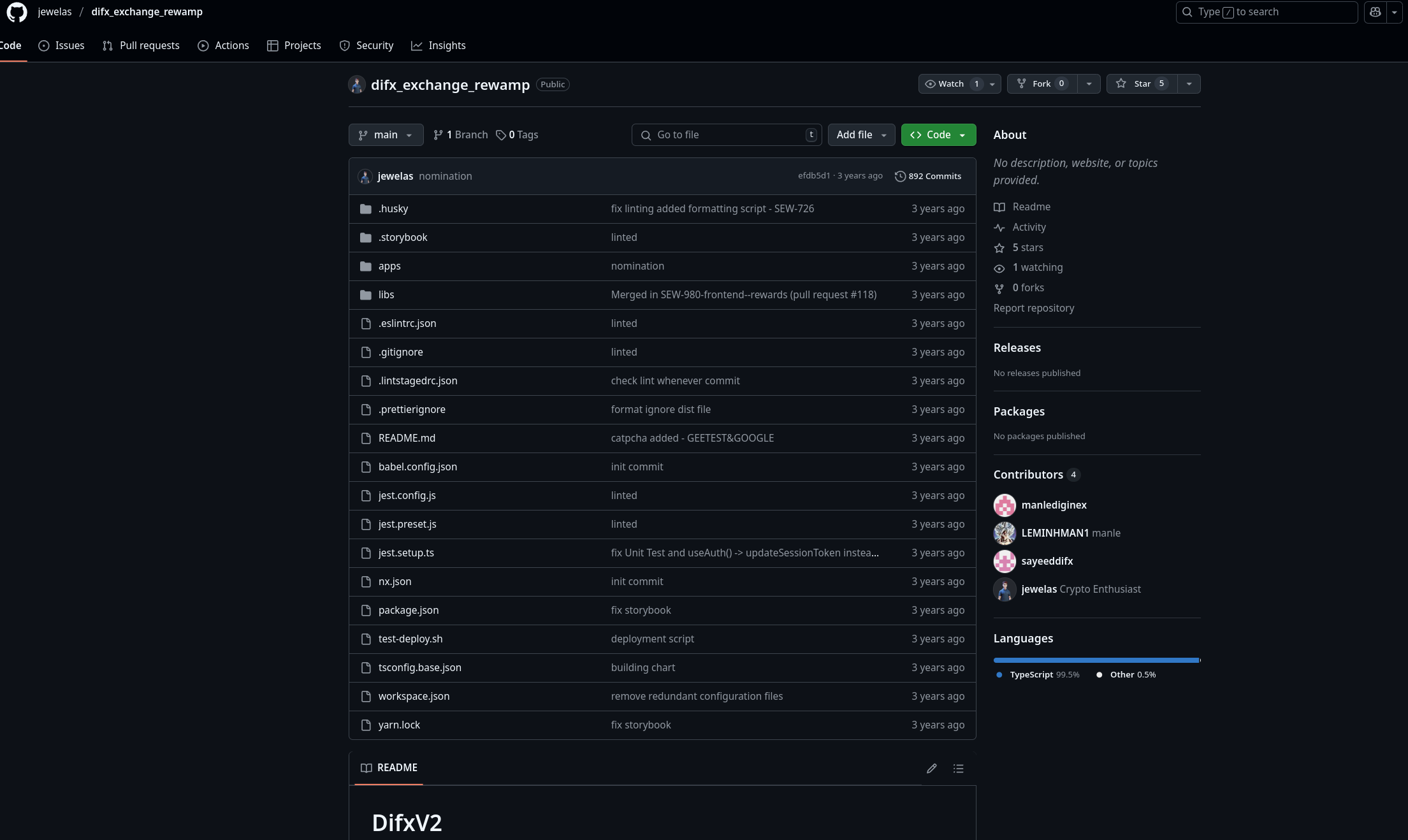
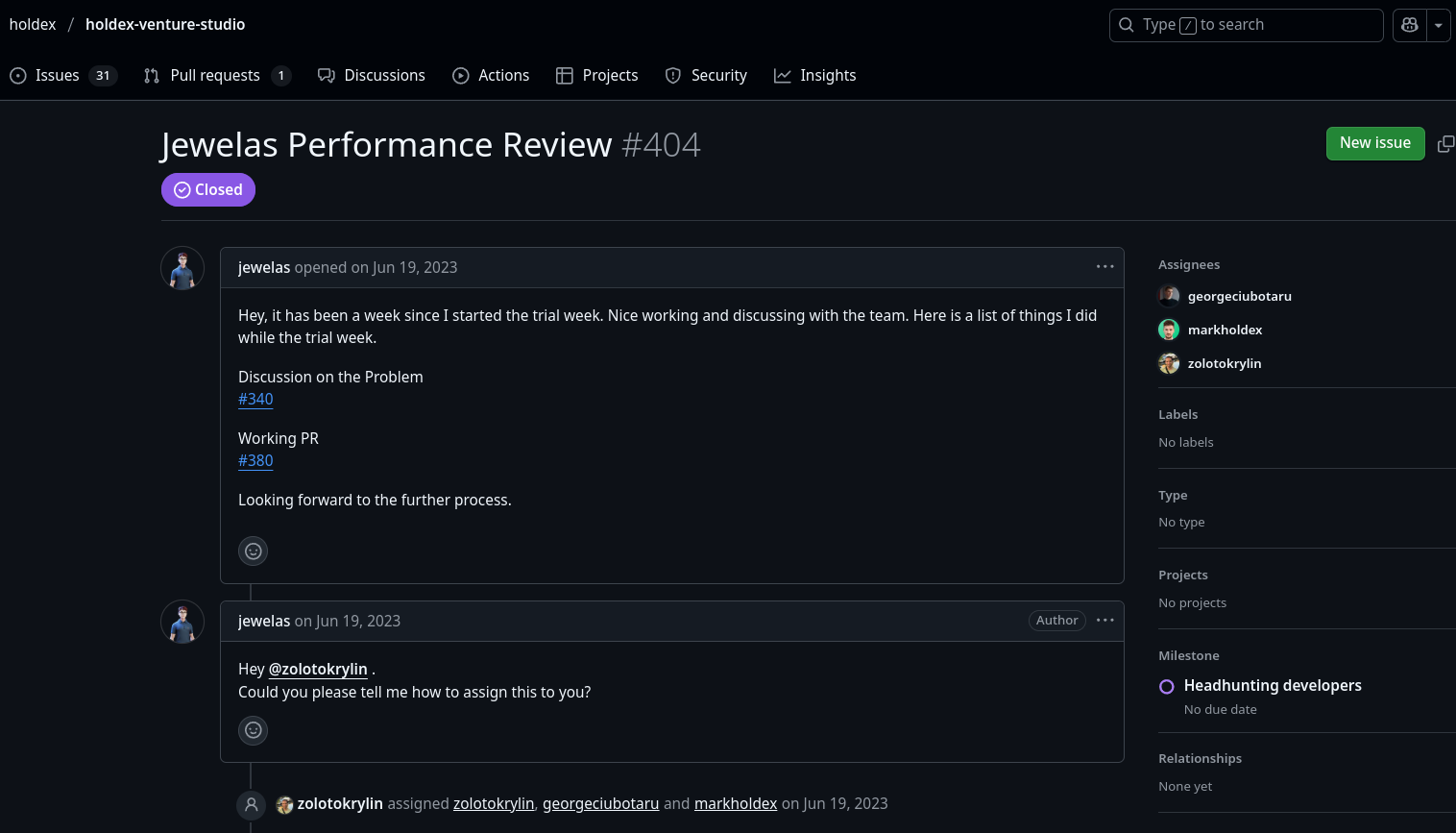
jewelas: Displays common DPRK IT worker characteristics. This actor is central to unveiling the remaining network of DPRK IT workers connected to the original0xNickLFranklinthreat actor.jewelasattempted to gain employment atholdexin 2023.- However, the strangest connection for
jewelasis to the potentially fraudulent CEXdifx.com. For reasons unknown,jewelashas access to the front-end code of thedifx.comwebsite. difx.comitself is a suspicious website, with multiple negative reviews claiming blocked withdrawals. Thedifx.comteam appears anonymous; the names of engineers listed on Crunchbase do not match email addresses found during the investigation.jewelaswas either hired by the CEX for front-end work, ordifx.comitself is a DPRK-run operation.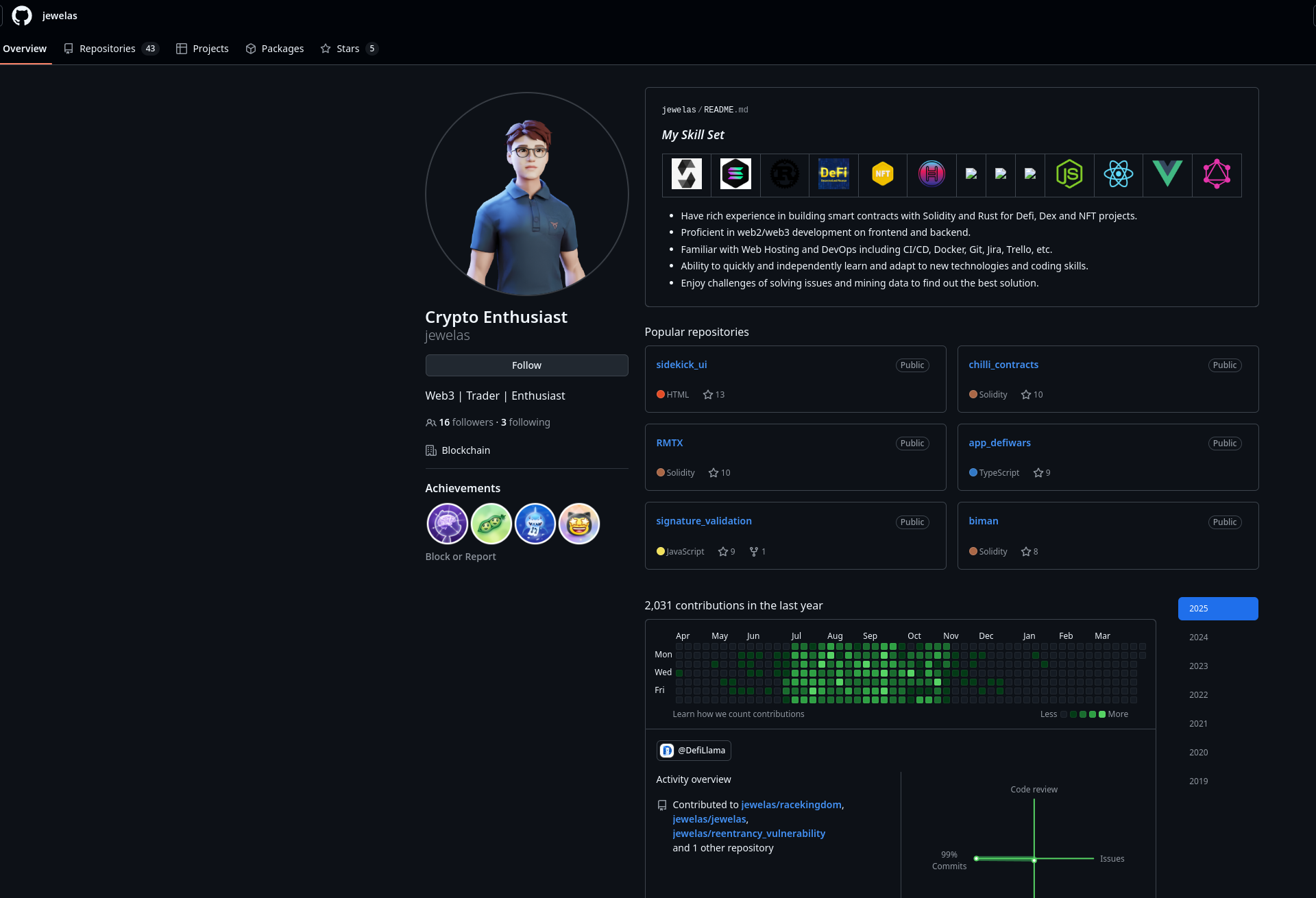
- However, the strangest connection for
Threat Summary
- AppleJesus:
NickLFranklinbuilt rapport in the security community to deliver malicious payloads.[0] - WageMole:
jewelasattempted to gain employment atholdex.comin 2023.[1] - Contagious Interview / AquaProtocol: A “fake” Web3 protocol seeded with nearly $800k USD in liquidity. Likely used for credibility building during malicious campaigns potentially involving spear-phishing engineers and investors (
NickLFranklin,SonataM,CrazyDream000).[2] - Fake Memecoin Landing Pages (Phishing): Used to steal credentials and scam retail investors (
SonataM). [3] - Fake Memecoin Landing Pages (Rug Pull): Used for direct theft (“rug pulling”) from retail investors (
SonataM).[4] - Unclear Connection to
difx.com: Potentially a DPRK-run CEX scam involvingjewelasor a DPRK IT Worker victim.[5]
[0] https://x.com/pcaversaccio/status/1905240537071833529
[1] https://github.com//holdex/holdex-venture-studio/issues/404
[2] https://x.com/blackbigswan/status/1905003274098417940
[3] https://liquina.vip/ fake website. The real website is https:/liquina.ai
[4] BERT on BSC is not the same as BERT on SOL, the original
[5] https://scambrokersreviews.com/crypto-scams/difx-review/
DPRK ScamPotting
Running scam/rugpull operations isn’t typically considered the modus operandi of the Central Committee of the Workers’ Party. Their actions are mostly attributed to deploying fake developers, insider threats, or malware-related campaigns. However, for some time now, we have observed many “scam-like” Web3 operations emerging with very particular characteristics.
Initially, we couldn’t attribute these activities to North Korean operations with high certainty. However, the 0xNickLFranklin debacle finally provided a strong indicator that such operations are indeed run by the DPRK. It’s worth noting that the primary goal of operations like Aqua Protocol is likely not the “scam” (rug pull) itself, but rather using them to boost credibility and establish an initial foothold for standard malware-delivery operations. It’s also consistent with 0xNickLFranklin behavior of looking to build business connections, among other things, with different Web3 protocols.
Essentially, these are honeypots run by the DPRK to lure legitimate developers and/or investors, establish initial credibility, and ultimately leverage that access for delivering malicious payloads. We’ve coined the term “ScamPotting” (Scam + Honeypot) to refer to this particular tactic.
At the same time, we observe DPRK-related operations reaching into every possible monetizable corner of the blockchain ecosystem – whether it’s spear-phishing for wallet access or executing straight rug pulls, funded by liquidity from previous hacking campaigns.
The important lesson here is not to blindly trust protocols or their engineers reaching out with offers, even if their codebase is on GitHub, they have deployed liquidity, they have undergone an auditing process, or even if they have common social network with you.
IOCs
Below is a list of identity-related flags for the threat actors discussed. It is safe to assume that any connection to the accounts listed below should be treated as a potential red flag during recruitment or due diligence processes.
(Note: The list of specific IOCs like GitHub accounts is already included in the main text above.)
SonataM
"created_at": "2024-06-23T15:07:34Z",
"updated_at": "2025-03-26T11:15:51Z"
"email": "crazy.dream0129@gmail.com","name": "SonataM"
"email": "mooneydev9001@gmail.com","name": "SonataM"
SonataM Phishing/RugPulls:
Note: the below list can be mixed with “legit” memecoin projects, it’s honestly extremely hard to tell what’s not a scam in this space. It’s possible that DPRK itself just copied non-DPRK scam etc.
1. cr900 - https://github.com/SonataM/cr900
1. Name Change from CRISTIANO RONALDO 900 to BERT on BSC
2. https://t.me/bertonbsc / https://t.me/cr900_portal
3. https://x.com/BERTonBSC / https://x.com/cr900_eth
4. https://www.dextools.io/app/en/token/bertonbsc?t=1743262255635solana/dd8elrwk1ebt3m4zn5c4asw1ky59phpbgzjbavsg7k2r
5. https://www.dextools.io/app/en/token/bertonbsc?t=1743262255635
6. 0xe77d3a178c9f15096e83e789a8049ef20cca1095
2. Liquina - https://github.com/SonataM/Liquina
1. https://x.com/liquinia_eth > https://x.com/liquina_eth > https://x.com/liquina_ai > https://x.com/lqna_erc20 (notice typo)
2. https://t.me/liquinia_eth > https://t.me/liquina_eth> https://t.me/liquina_ai > https://t.me/lqna_erc20 (notice typo)
3. https://dexscreener.com/ethereum/0xd9e6f484f5cb1141383299c303841eb2080a4f57 (FAKE)
4. https://dexscreener.com/ethereum/0x47597113c0d3cb6d6c9a0f6ba90d5f73b431b58f (RUG PULL. Website https://liquina.vip/ - hosted on vercel like GH deployments. The real web is https:/liquina.ai)
3. trumpx - https://github.com/SonataM/trumpx (0xComingSoon)
1. trumpx-dusky.vercel.app
2. https://x.com/trumpx_erc20
3. https://t.me/trumpx_channel
4. brics - https://github.com/SonataM/brics (0xComingSoon)
1. brics-phi.vercel.app
2. https://x.com/brickbrosETH/
3. t.me/brickbrosETH
5. trumpshair - https://github.com/SonataM/trumpshair
1. trumpshair.vercel.app
2. https://x.com/trumpshairETH
3. https://t.me/trumpshairETH
4. https://www.dextools.io/app/en/ether/pair-explorer/0x62fd37d24a2e76881e597da9ab3d51b1fa11f580?t=1732104771243
5. https://dexscreener.com/ethereum/0x1c00abc3869971870025b7bfffb98dac80d314cf
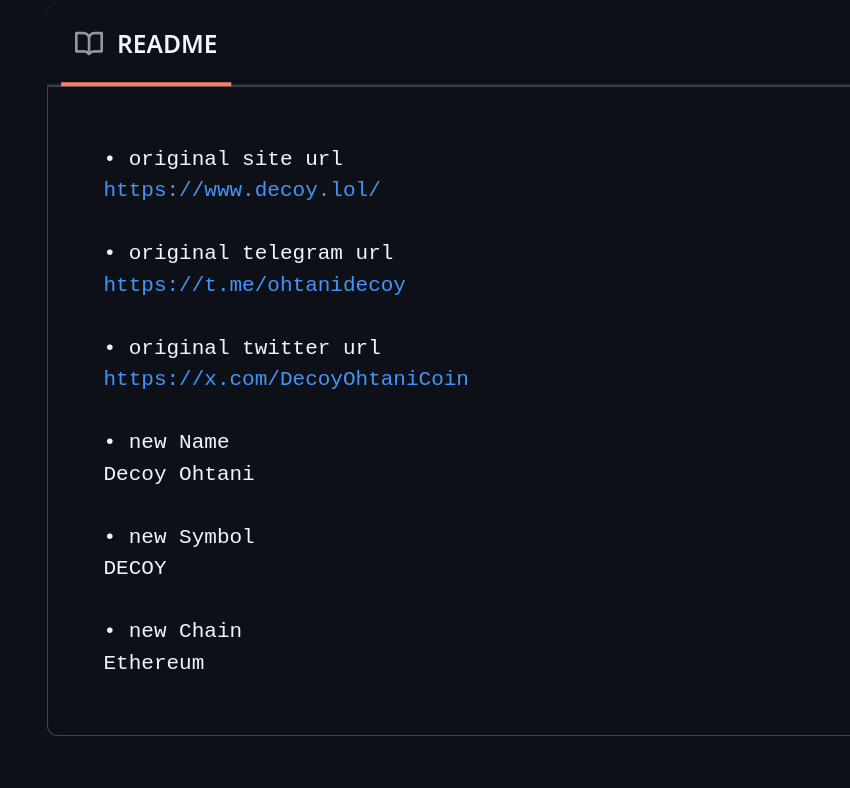
6. decoy - https://github.com/SonataM/decoy
1. https://decoy-nu.vercel.app/
2. https://www.dextools.io/app/en/ether/pair-explorer/0x52aE2BD7016c292Ed75d265E84d90Faa7A4a3113?t=1716574755333
3. https://dexscreener.com/ethereum/0x52aE2BD7016c292Ed75d265E84d90Faa7A4a3113
4. https://x.com/decoy_eth (from readme, original: https://x.com/DecoyOhtaniCoin)
5. https://t.me/decoy_eth (from readme, original: https://t.me/ohtanidecoy)
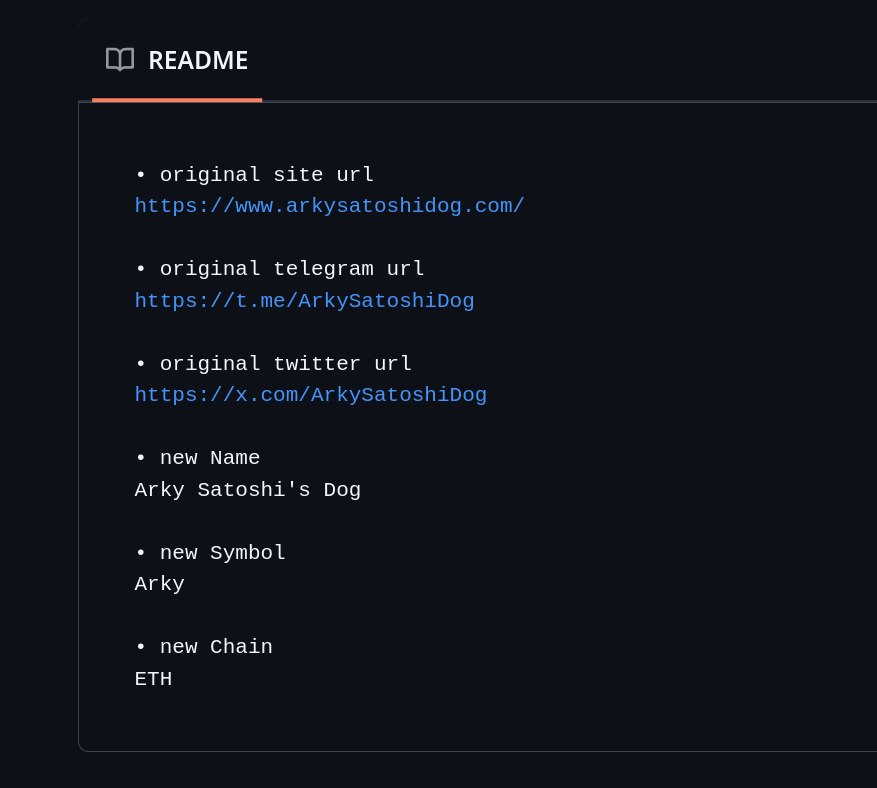
7. arky - https://github.com/SonataM/arky
1. https://arky-drab.vercel.app/
2. https://dexscreener.com/ethereum/0x4616D9B986da6fc6a1D53f2adfc45169B47757E8
3. https://x.com/arkyErc20
4. https://t.me/arkysatoshisdog (notice typo)
8. orken - https://github.com/SonataM/orken/
1. https://orken.vercel.app/
2. https://x.com/orkenErc20
3. https://t.me/orkenErc20
9. louie - https://github.com/SonataM/louie (0xComingSoon)
1. https://louie-iota.vercel.app/
2. https://www.louieraccoon.com/ / https://x.com/LouieCTOSol (info.txt, org names)
3. https://x.com/louieoneth
4. https://t.me/louieoneth
10. vodcat - https://github.com/SonataM/vodcat (0xComingSoon)
1. https://vodcat-self.vercel.app/
2. https://x.com/vodcatcoinerc20
3. https://t.me/vodcat_channel
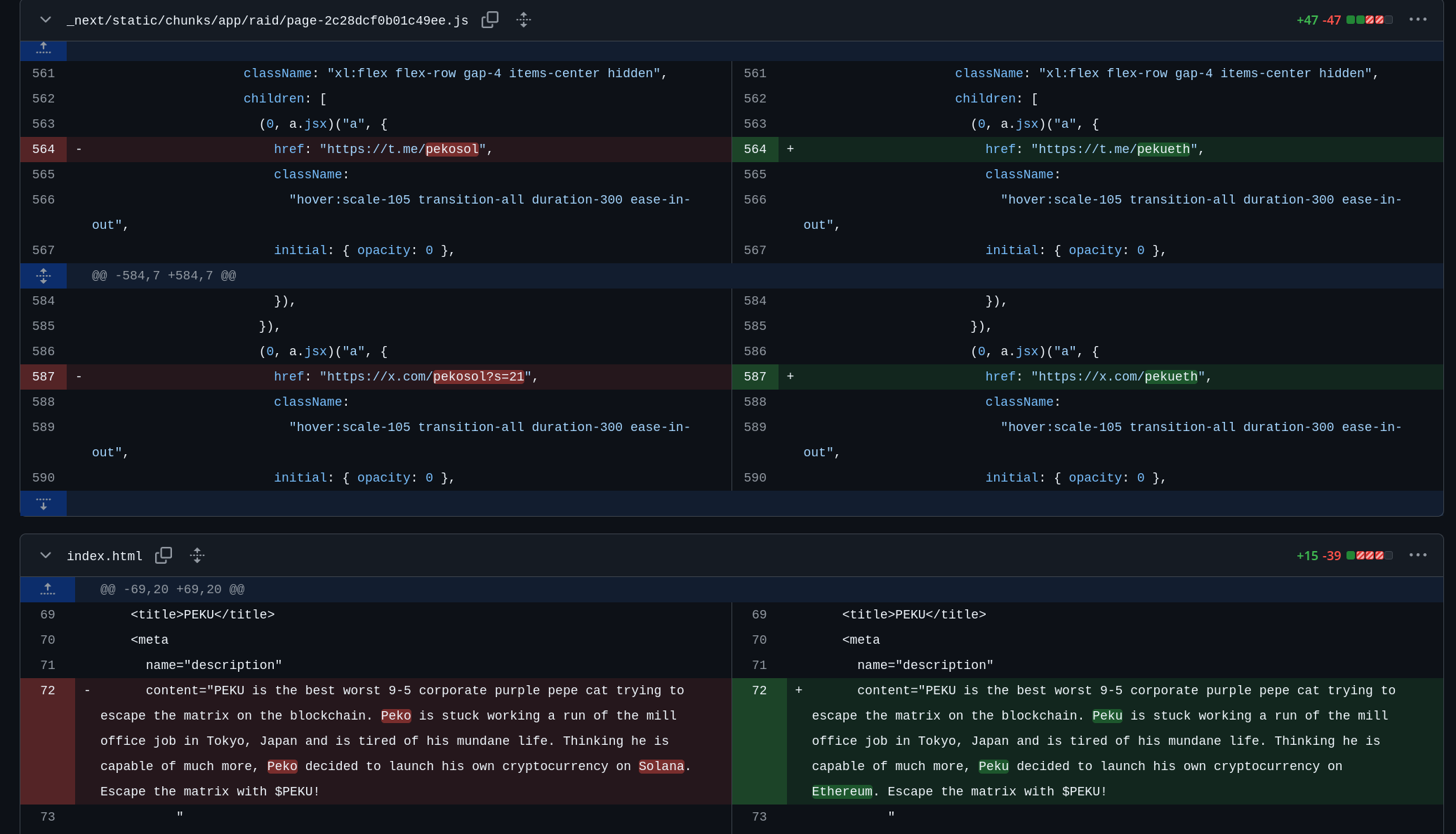
11. peku - https://github.com/SonataM/peku
1. https://peku.vercel.app/
2. Impersonating #Peko (typo - Peku)
3. Change of network from SOL to ETH
4. https://t.me/pekueth
5. https://x.com/pekueth
12. ufobirddog - https://github.com/SonataM/ufobirddog
1. https://ufobirddog.vercel.app/
2. https://dexscreener.com/ethereum/0x5239F8233f80f9c43463e0faA53B345214A1E9dD / https://www.dextools.io/app/en/ether/pair-explorer/0x5bd3586034413a1abcd4ca684893af720903b5ac?t=1719322848714
3. info.txt - original: https://www.steveerc.com/ / https://x.com/Ethereum_Steve
4. Original address? https://dexscreener.com/ethereum/0x4206921bf8b68dd28282206a5c1486c359df46c9
5. https://t.me/ubd_portal
6. https://x.com/ufo_bird_dog
7. https://t.me/Steve420erc (original?)
13. moocat - https://github.com/SonataM/Moocat
1. Abandoned? Tried to port from SOL to ETH, see screenshot
CrazyDream000
"created_at": "2023-02-23T14:14:04Z",
"updated_at": "2025-03-11T04:28:42Z"
"old_usernames": "deleted_username": ["Dima0dev","mooney0129"],
"email": "126175765+CrazyDream000@users.noreply.github.com","name": "CrazyDream"
"email": "126175765+CrazyDream000@users.noreply.github.com","name": "Dima!!"
"email": "126175765+CrazyDream000@users.noreply.github.com","name": "Ryan Jacks"
"email": "126175765+Dima0dev@users.noreply.github.com","name": "Dima"
"email": "126175765+Dima0dev@users.noreply.github.com","name": "Mooney"
"email": "126175765+dima0dev@users.noreply.github.com","name": "Dima!!"
"email": "126175765+mooney0129@users.noreply.github.com","name": "MooneyDev"
"email": "126175765+mooney0129@users.noreply.github.com","name": "mooney0129"
"email": "danakimoto319@gmail.com","name": "CrazyDream000"
"email": "danakimoto319@gmail.com","name": "crazydream000"
"email": "mooneydev9001","name": "mooney0129"
"email": "mooneydev9001@gamil.com","name": "mooney0129"
"email": "mooneydev9001@gmail.com","name": "CrazyDream000"
"email": "mooneydev9001@gmail.com","name": "Dima0dev"
"email": "mooneydev9001@gmail.com","name": "SonataM"
"email": "mooneydev9001@gmail.com","name": "crazyDream000"
"email": "mooneydev9001@gmail.com","name": "crazydream000"
"email": "mooneydev9001@gmail.com","name": "dima0dev"
"email": "mooneydev9001@gmail.com","name": "mooney0129"
"email": "mooneydev9001@gmail.com","name": "sonataM"
"email": "121175573+jewelas@users.noreply.github.com","name": "Shooter"
"email": "126177355+AngrySusanoo@users.noreply.github.com","name": "AngrySusanoo"
"email": "126177355+SusanoO-O@users.noreply.github.com","name": "SusanoO"
"email": "oleksandr.sytnikov0413@gmail.com","name": "Theodor Nakajima"
"email": "wind.shadow1004@gmail.com","name": "AlterShow"
Contributors to CrazyDream00 repositories:
CryptoSenju, jewelas
Mutual followers:
codeninja819,goldnite,zdeiby,kahangahanga,ThecoderPinar,spiderman128,smartman0307,mustafacagri,teddy3728,cupidbow20000,imhere4uu,Ydev1992,whimsicaldev1203,burnt-exe,K-NRS,coachee0103,kenjinote,GoldLuckyK,FullStackStar,kyomano,Israruddin293,whitedaisy7,robotant8888,keiru517,OlekSytn,AppServiceProvider,cumsoft,pyking319,paladin0742
Jewelas
"created_at": "2022-12-21T13:39:06Z",
"updated_at": "2025-03-25T10:06:01Z"
"email": "121175573+jewelas@users.noreply.github.com","name": "Crypto Enthusiast"
"email": "121175573+jewelas@users.noreply.github.com","name": "Shooter"
"email": "jewelas.tm@gmail.com","name": "jewelas"
"email": "126131584+monster223223@users.noreply.github.com","name": "Kay Akira"
"email": "126175765+Dima0dev@users.noreply.github.com","name": "Dima"
"email": "atos980411@gmail.com","name": "AtosDev"
"email": "cloverdev88@gmail.com","name": "AtosDev"
"email": "cloverdev88@gmail.com","name": "unknown"
"email": "superdev4837@gmail.com","name": "superdev4837"
Contributors to jewelas repositories:
monster223223, Dima0dev (Other identity of SonataM/CrazyDev000, deleted), AtosDev (AtosLABs now), cloverdev88 (deleted), superdev4837, sup3reric, meloket, CrazyDream000
Mutual following:
OlekSytn
Starring:
Naruto-Leader